Data Protection News: Latest Trends, Regulations, and Technologies in 2026

In the modern digital economy, data has become one of the most valuable assets for organizations. Companies collect massive volumes of personal, financial, and behavioral data every day. However, the rise of cyberattacks, ransomware incidents, and data breaches has intensified the need for robust data protection frameworks. As a result, data protection news has become a crucial topic for IT leaders, regulators, enterprises, and individuals.
Over the last few years, global governments and technology organizations have introduced stricter policies and advanced cybersecurity technologies to protect digital information. From new privacy laws to advanced encryption techniques and AI-powered security tools, the data protection landscape is evolving rapidly.
This article explores the latest data protection news, emerging security technologies, global regulations, industry statistics, and enterprise strategies shaping the future of digital privacy and cybersecurity.
Understanding Data Protection
Data protection refers to the strategies, technologies, and policies used to safeguard digital information from unauthorized access, corruption, theft, or loss. It covers both organizational practices and regulatory frameworks designed to ensure that personal and business data remains secure.
Core Objectives of Data Protection
- Protect sensitive information from cyberattacks
- Maintain data confidentiality and integrity
- Ensure regulatory compliance with privacy laws
- Prevent financial losses from breaches
- Build consumer trust in digital services
Organizations today rely on several mechanisms such as encryption, identity management, access control, and secure backups to ensure strong data protection.
Why Data Protection News Matters in 2026
The global cybersecurity landscape is evolving rapidly. Businesses are dealing with increasingly sophisticated threats such as AI-powered phishing, ransomware-as-a-service, and supply chain attacks.
Keeping up with data protection news helps organizations:
- Stay compliant with evolving privacy regulations
- Adopt modern cybersecurity technologies
- Prevent costly data breaches
- Improve data governance practices
- Understand industry risks and emerging threats
According to cybersecurity industry estimates, the global cost of cybercrime may exceed $10 trillion annually by 2026, making data protection a top priority for enterprises.
Major Data Protection Trends in 2026
Several technological and regulatory trends are shaping modern data protection strategies.
-
AI-Driven Cybersecurity
Artificial Intelligence has become a major tool for detecting anomalies and preventing cyber threats. Security platforms now use machine learning to analyze network activity and identify suspicious patterns in real time.
Benefits include:
- Faster detection of threats
- Automated response to attacks
- Reduced human error in security operations
- Improved incident response times
However, attackers are also using AI tools to develop more sophisticated cyberattacks, which is increasing the cybersecurity arms race.
-
Zero-Trust Security Architecture
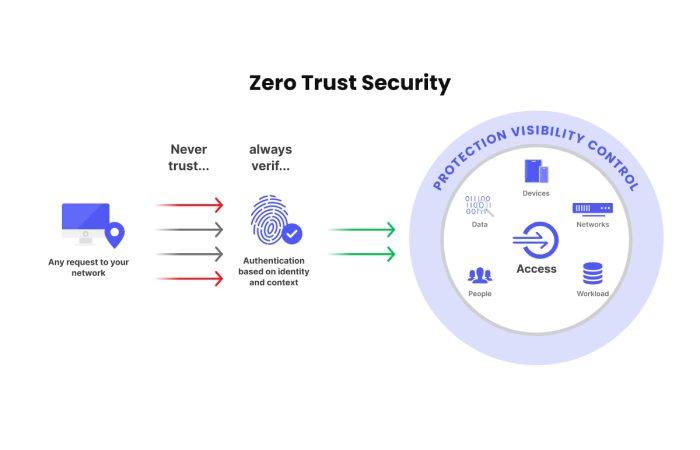
Traditional network security models relied on perimeter defenses. Modern organizations are shifting toward Zero Trust Architecture (ZTA).
The core principle of Zero Trust is “never trust, always verify.”
Key features include:
- Continuous identity verification
- Least-privilege access control
- Micro-segmentation of networks
- Real-time security monitoring
Zero-trust frameworks are now widely adopted by enterprises and government agencies.
-
Data Privacy Regulations Expanding Worldwide
Global regulators are introducing stricter laws to protect consumer data.
These regulations define how companies collect, process, and store personal information.
Major Data Protection Regulations
| Regulation | Region | Key Focus | Penalties |
| GDPR | European Union | Personal data protection and consent | Up to €20 million or 4% of annual revenue |
| CCPA / CPRA | United States (California) | Consumer privacy rights | Up to $7,500 per violation |
| DPDP Act | India | Digital personal data protection | Significant financial penalties |
| PIPL | China | Personal data handling and cross-border transfer | Large financial penalties |
These frameworks are forcing companies to redesign their data governance and compliance programs.
-
Rise of Cloud Data Protection
Cloud computing adoption has grown rapidly as organizations migrate workloads to platforms such as AWS, Microsoft Azure, and Google Cloud.
However, cloud environments require specialized security strategies.
Important cloud protection measures include:
- Data encryption in transit and at rest
- Secure cloud configuration management
- Multi-factor authentication
- Continuous monitoring of cloud workloads
Companies are increasingly investing in Cloud Security Posture Management (CSPM) tools to identify misconfigurations and vulnerabilities.
Global Data Breach Statistics
Recent cybersecurity reports show a significant increase in data breaches across industries.
Data Breach Impact by Industry
| Industry | Average Breach Cost (USD) | Common Attack Type |
| Healthcare | $10.9 million | Ransomware |
| Finance | $5.9 million | Phishing |
| Technology | $5.1 million | Insider threats |
| Retail | $3.3 million | Credential theft |
| Government | $2.9 million | Nation-state attacks |
Healthcare organizations face the highest breach costs due to sensitive patient data and regulatory penalties. (IBM)
Data Protection Technologies Used by Enterprises
Organizations now deploy multiple security technologies to protect digital assets.
Core Data Protection Technologies
| Technology | Purpose | Benefits |
| Encryption | Protects stored and transmitted data | Prevents unauthorized access |
| Data Loss Prevention (DLP) | Prevents sensitive data leaks | Improves regulatory compliance |
| Identity and Access Management (IAM) | Controls user access | Reduces insider threats |
| Backup and Disaster Recovery | Recovers data after attacks | Ensures business continuity |
| Endpoint Security | Protects devices and endpoints | Stops malware and ransomware |
A layered approach combining these technologies provides defense-in-depth protection.
Price Comparison of Data Protection Solutions
Businesses invest heavily in cybersecurity platforms. The cost varies depending on features, scalability, and deployment model.
Popular Data Protection Platforms
| Platform | Deployment | Starting Price | Best For |
| Veeam Backup | Hybrid / Cloud | $400 per year | Data backup and recovery |
| Acronis Cyber Protect | Cloud | $85 per user per year | Backup + anti-malware |
| Druva Data Security Cloud | Cloud | $210 per user annually | Enterprise cloud backup |
| Commvault | Hybrid | Custom pricing | Large enterprises |
| Rubrik Security Cloud | Cloud | Custom pricing | Ransomware protection |
Organizations often compare pricing based on:
- Number of users
- Storage requirements
- Backup frequency
- Recovery speed
- Compliance features
Data Protection Market Share
The global data protection market is expanding rapidly due to increasing cyber threats and compliance requirements.
Market Distribution of Data Protection Solutions
| Segment | Market Share |
| Cloud Data Protection | 35% |
| Endpoint Protection | 20% |
| Data Loss Prevention | 15% |
| Backup and Recovery | 18% |
| Identity Security | 12% |
Pie Chart Representation

This distribution highlights the growing demand for cloud-based security solutions.
Key Challenges in Data Protection
Despite technological advancements, organizations still face several challenges when protecting data.
- Increasing Cyber Threat Complexity
Modern cyberattacks use automation, AI, and social engineering techniques, making them difficult to detect.
- Data Growth
The exponential growth of digital data makes it harder for companies to manage and secure all information assets.
- Compliance Complexity
Companies operating globally must comply with multiple regulations, each with different requirements.
- Insider Threats
Employees and contractors may unintentionally or intentionally leak sensitive data.
- Legacy Systems
Older infrastructure often lacks modern security capabilities, increasing vulnerability. (NIST)
Best Practices for Effective Data Protection
Organizations should adopt a comprehensive strategy that includes people, processes, and technology.
Data Protection Best Practices
- Implement multi-factor authentication (MFA) across systems
- Encrypt sensitive data both at rest and in transit
- Conduct regular security audits and vulnerability assessments
- Maintain secure backups to prevent ransomware damage
- Train employees about phishing and cybersecurity awareness
- Use Zero Trust security models for network protection
Companies that follow these best practices significantly reduce their risk of data breaches.
Role of Artificial Intelligence in Data Protection
Artificial intelligence is becoming central to modern cybersecurity strategies.
AI Applications in Data Protection
- Threat detection using behavioral analytics
- Automated incident response systems
- Fraud detection in financial transactions
- Malware identification using pattern recognition
- Predictive analytics for security risks
Security analysts are increasingly relying on AI-powered security operations centers (SOCs) to handle massive volumes of threat data.
Data Protection News Impact on Businesses
Recent developments in the cybersecurity industry are forcing companies to rethink their security strategies.
Business Impacts
- Increased cybersecurity budgets
- Higher demand for security professionals
- Greater focus on compliance and governance
- More adoption of cloud security platforms
- Integration of AI and automation tools
Many organizations now allocate 10–15% of their IT budgets to cybersecurity, reflecting the importance of protecting digital assets.
Future of Data Protection
Looking ahead, several developments are expected to shape the future of data security.
Emerging Innovations
- Quantum-resistant encryption
- Privacy-enhancing computation
- Decentralized identity systems
- Confidential computing
- Blockchain-based data integrity verification
These technologies aim to strengthen data protection while maintaining privacy and transparency.
How Organizations Can Stay Updated with Data Protection News
To remain secure and compliant, businesses must continuously monitor industry developments.
Reliable Sources for Data Protection Updates
- Cybersecurity research firms
- Government regulatory announcements
- Security vendor reports
- Industry conferences and webinars
- Technology news platforms
Security teams should integrate threat intelligence platforms to stay ahead of emerging risks.
Conclusion
Data protection has become one of the most critical aspects of modern digital infrastructure. With increasing cyber threats, stricter regulations, and rapid technological innovation, organizations must adopt comprehensive cybersecurity strategies to safeguard sensitive information.
The latest data protection news highlights the growing importance of technologies such as AI-driven threat detection, zero-trust architecture, cloud security solutions, and advanced encryption. At the same time, governments worldwide are introducing stricter privacy regulations that require organizations to improve their data governance practices.
Businesses that prioritize data protection not only reduce the risk of costly breaches but also build stronger trust with customers and partners. As digital transformation continues to accelerate, robust data protection frameworks will remain essential for ensuring security, compliance, and long-term business resilience.
